‘Artificial Intelligence’ scholarship for IUE graduate Mert
Mert Atanmış (23), who graduated from Izmir University of Economics (IUE) Department of Industrial Engineering with the first place last ...

He became the European champion while trying to lose weight
Yağız Hacılar, a student at Izmir University of Economics (IUE) Department of Industrial Engineering, became the European champion twice in ...

A 'digital' model for the construction industry
Sadık Onur Özden and Tunç Çokuysal, students of Izmir University of Economics (IUE), turned the demand for digitalization in the ...

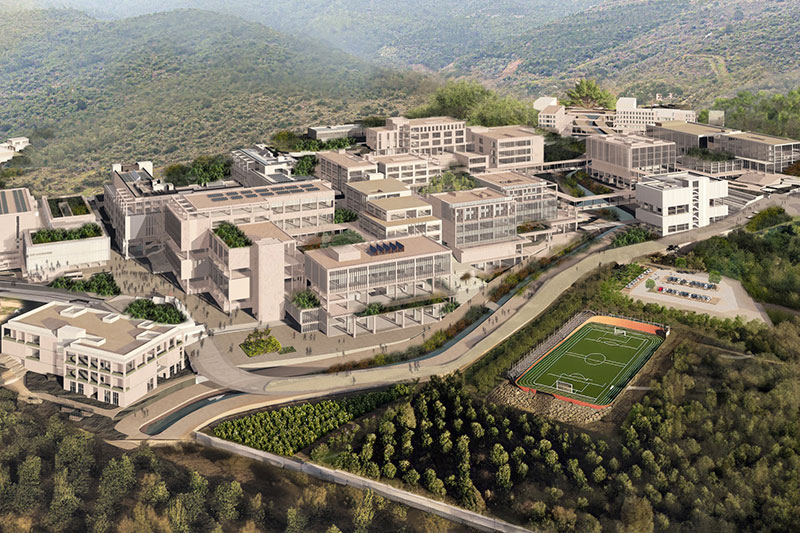
Faculty 101
Industrial Systems Society organized the Faculty101 seminar in our school for the students who begin to the Industrial Engineering Department ...
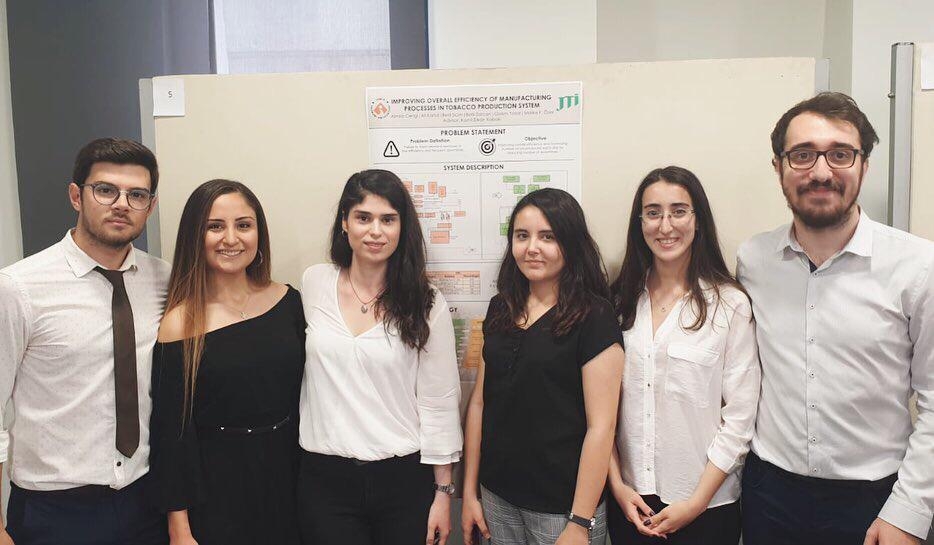
Industrial Engineering Department Graduation Project Exhibition was held on May 20th.
...

Industry 4.0 training was held between November 6-8 .
...

Industrial Engineering Department Graduation Project Exhibition was held on May 11th.
...